User authentication§
In the previous example, we've reused the Warpgate's admin user, which only had a password as its only way to authenticate. Warpgate supports passwords, public keys, authenticator apps, SSO (OIDC), API tokens and combinations thereof as authentication methods.
Changing a user's password§
Log into the Warpgate admin UI and navigate to Config > Users > admin, delete the old password and click Add password to add a new one.
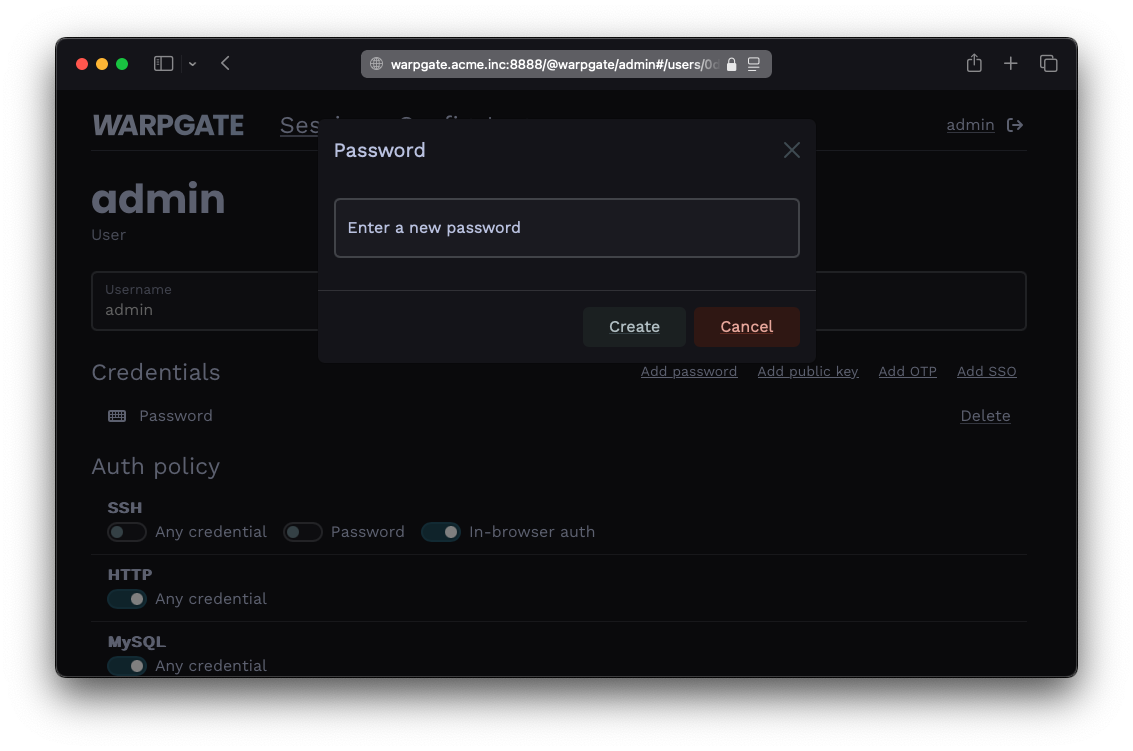
Adding a password
Users can also manage their own password by clicking their username in the top right corner. This can be globally disabled via Config > Global parameter.
Adding a public key for a user§
- Grab the user's public key in OpenSSH format (normally, you can just copy the
~/.ssh/id_<type>.pubfile contents), e.g.:
ssh-ed25519 AAAAC...bD4I user@host
- Click
Add public keyand paste it:
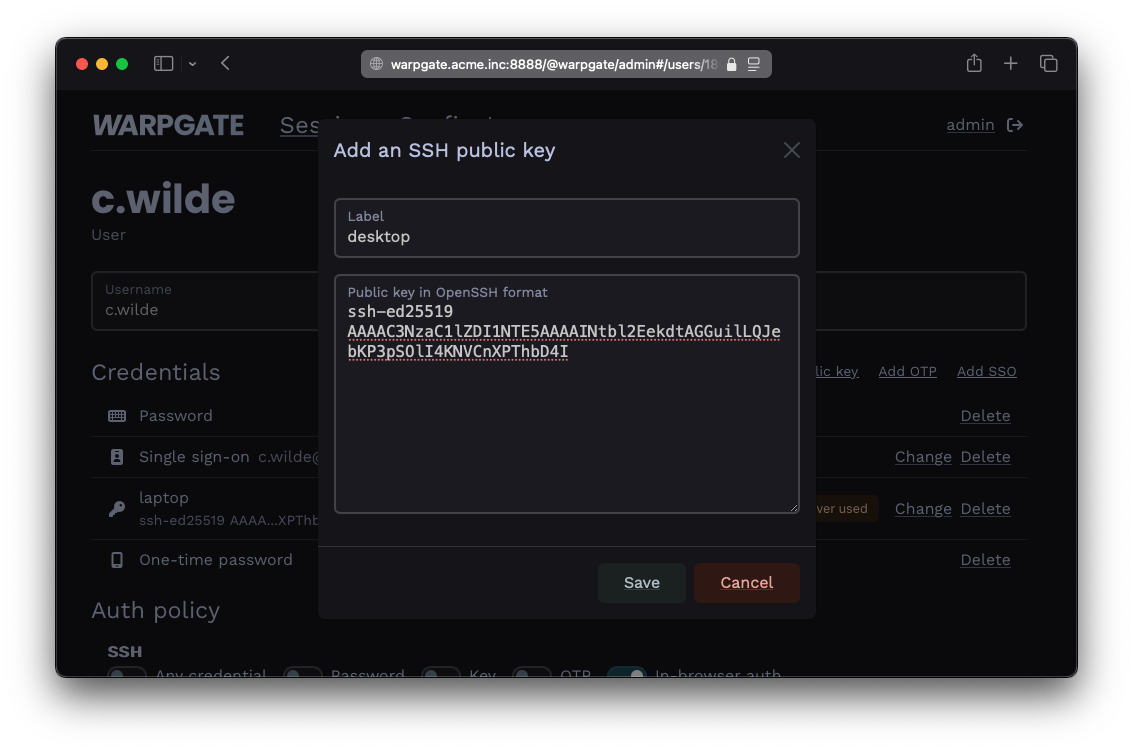
Adding a public key
Adding a client certificate for a user§
Warpgate supports client certificates for authentication over the Kubernetes API protocol.
- Click
Issue certificateand Warpgate will generate a keypair in-browser and issue a client certificate for the user:
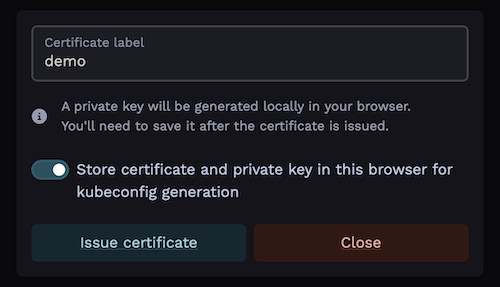
Issuing a client certificate
Note the option to store the private key in the browser's local storage for later use. This allows the Warpgate frontend to later retrieve the private key to generate a kubeconfig file for the user.
- The key must be stored in the same browser that the user will be getting connection instructions on.
- Obviously, do not store the key in an untrusted environment.
- The key is stored in the browser's IndexedDB and can be deleted by "clearing browser data" or similar.
- If the key is not stored at the time of certificate generation, Warpgate will generate a
kubeconfigwith placeholders in it. - It's not possible to store the private key after the fact; the user will always have an option of simply issuing a new certificate ad-hoc and storing its key (as long as credential self-management is allowed).
- The private key is never sent over the network.
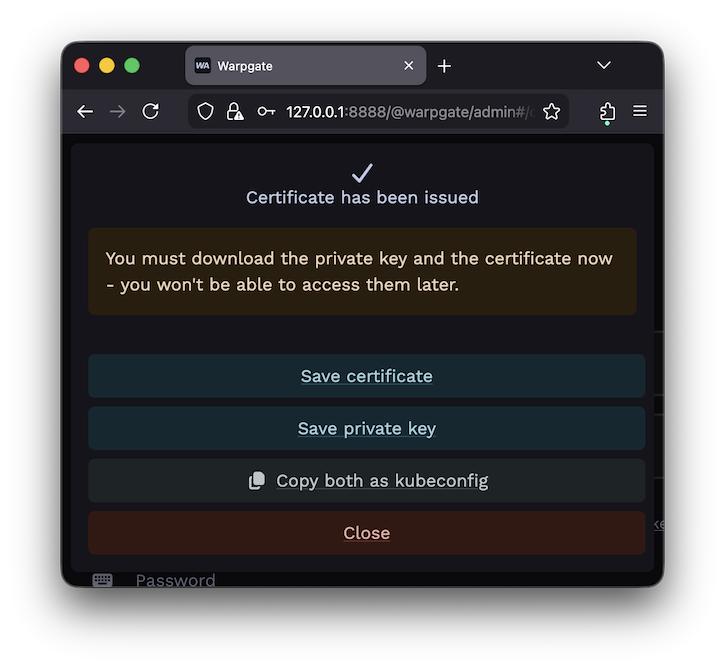
Certificate is issued
Requiring multiple authentication factors§
Warpgate can require a client to present both a public key and a password.
- In the
Auth policy>SSHsection, uncheckAny credentialand select bothPasswordandKey:
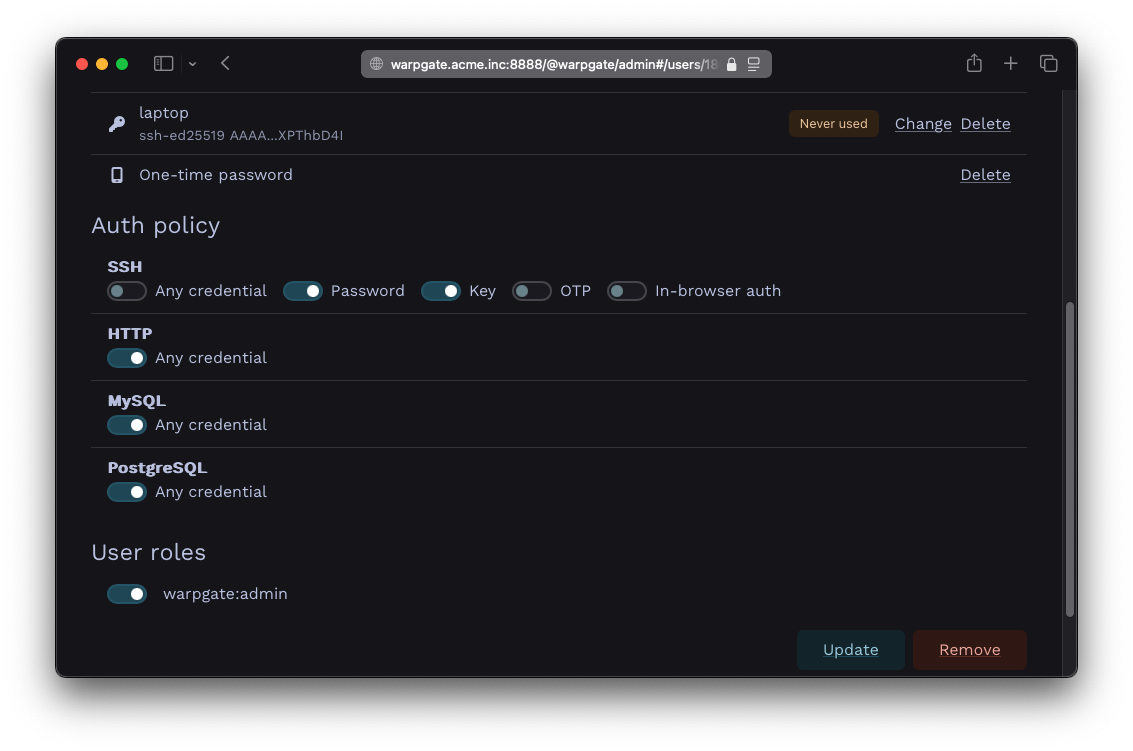
Setting up a multifactor auth policy
SSH client authentication methods§
Warpgate allows you to globally block SSH authentication methods. This can be useful if you exclusively use public key authentication and would like to prevent network scanners from hammering password authentication on a public port. By default, all methods are enabled.
You can disable them individually under Config > Global parameters > SSH authentication methods:
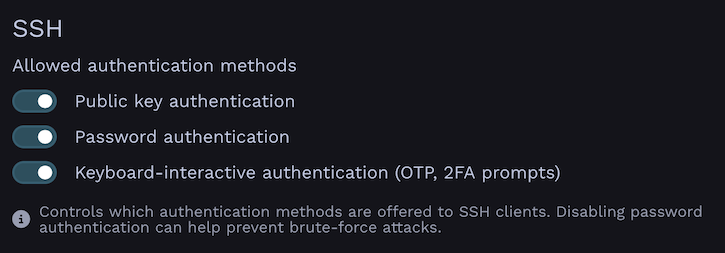
SSH authentication methods configuration in Global Parameters
API Tokens§
Warpgate supports API tokens for programmatic access. Users can create and manage their own API tokens through the web interface by clicking their username in the top right corner and navigating to the "API Tokens" section.
Requests made with an API token are considered authenticated in the same way as if the user would have logged in normally.
Using API Tokens§
Pass the token in the x-warpgate-token header when making API requests:
# Example: Get server info
curl -H "x-warpgate-token: xyz" https://warpgate.acme.inc/@warpgate/api/info